Israeli Spying After Epstein

The Corbett Report
The verdict is in: Epstein was a spy!
And, despite what the MSM says, he wasn’t making Kompromat for his KGB komrades so much as he was wheeling and dealing for his friends, the Israelis.
In addition to the many, many ties to Israel I listed in my 10 Things I Learned from the Epstein Files editorial, more and more data continues to emerge showing how Epstein worked with his pal (and ex-Israeli Prime Minister) Ehud Barak to secure contracts and achieve diplomatic objectives for Israel. This data includes information on how Epstein:
- helped Barak sell Israeli-produced, Gaza-tested biometric control systems to the Nigerian government;
- connected Barak and Israeli Prime Minister Benjamin Netanyahu with US investors seeking to exploit the Leviathan natural gas field west of Haifa;
- greased the skids for the first visit of an Indian Prime Minister to Israel and was asked to facilitate contact between Indian leadership and Trump administration insiders like Jared Kushner and Steve Bannon;
- used his political network and financial influence to broker a security cooperation agreement between Israel and Mongolia;
- &c.
Heck, the Israeli government even installed and maintained the security system at the Manhattan apartment Epstein frequently lent out to Barak.
Yes, whatever else Epstein may have been doing, it seems he was working diligently behind the scenes as an agent of influence to promote Israeli interests around the world.
But Epstein is dead, as you may have heard. So, how will Israel wield power and influence over foreign diplomats and businessman now that they can no longer rely on their favourite fixer?
As it turns out, we can catch glimpses of the answer to that question in the Epstein files, too…
THE CARBYNE CREW

Last November, the San Francisco Standard published “Inside the extended courtship linking Jeffrey Epstein, Peter Thiel, and Israeli officials.” The article details how Handala (an “Iran-linked hacking group”) obtained emails from Israeli officials that show that Epstein was once again the lubricant greasing the skids for the Israeli deep state in their attempt to woo the Silicon Valley broligarchs.
First, Epstein courted Thiel:
By 2014, Epstein had a relationship with Thiel. The two had at least three meetings scheduled in September of that year alone, according to copies of Epstein’s calendar obtained by The New York Times.
In hindsight, they were getting into business together: In the year or so after these meetings, Epstein put $40 million into Valar Ventures, a firm Thiel cofounded, according to The New York Times. Thiel has not been accused of any wrongdoing in connection with his relationship with Epstein.
Then, he introduced Thiel to Barak:
In 2014, Epstein was eager to connect his two contacts, urging Barak over email to have dinner with Thiel. Barak eventually agreed to Epstein’s overture, and, according to emails he sent to friends, had dinner with the Palantir cofounder in June 2014.
So, what became of this relationship?
As Drop Site News reported last month, Epstein immediately used this connection to sell Thiel on Carbyne, an Israeli firm providing “video streaming and geolocation software for emergency services” around the world.
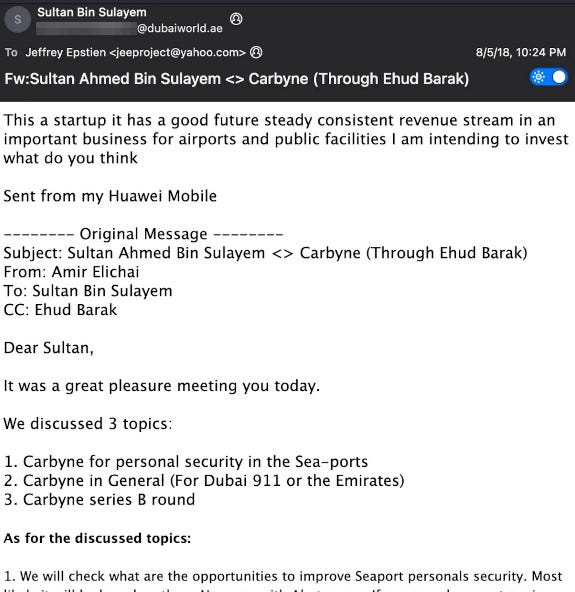
Originally called “Reporty,” Carbyne didn’t just receive funding from Epstein. The company wasn’t just chaired by Barak. It didn’t simply boast Sultan Ahmed bin “loved the torture video“ Sulayem among its investors. It also just happened to be founded by Amir Elichia, a veteran of Israel’s cyberspook signals intelligence service, Unit 8200.
Sulayem forwarded an email from Elichai, a veteran of Israel’s Unit 8200 signals intelligence unit, proposing Sulayem’s participation in Carbyne’s Series B fundraising round that year. After meeting with Epstein and Barak, Peter Thiel had also invested in the round. Epstein introduced Barak and Elichai to one of Thiel’s venture funds while helping Barak develop relations with senior security officials in Mongolia. (Those talks had blossomed into a formal security agreement between Israel and Mongolia in 2017, which included plans for integrating Carbyne into the Mongolian emergency service.)
In other words, Epstein turns out to be the connecting point between the Israelis, the financiers, the Big Tech cartel and various foreign governments.
None of this is news to those who followed Whitney Webb’s reporting on the subject back in 2019, of course. But the recently released Epstein files contain more information on these connections, including the actual correspondence between Epstein, Barak, Thiel, Sulayem and the other people involved in this venture as well as the actual documents they were examining.
The story of Carbyne—an Israeli intelligence-founded and Israeli-backed company seeking to worm itself into the emergency response systems of countries around the world, including the US—is important in and of itself. Those interested in exploring the subject really owe it to themselves to read Webb’s original reporting on the topic from 2019.
But the Carbyne saga is not just interesting in and of itself. It’s interesting for what it tells us about the nature of spying in the 21st century.
Firstly, it provides a window into the story of Unit 8200, Israel’s infamous cyberspy team.
THE 8200 GANG

As noted above, Carbyne’s founder and CEO was Amir Elichai.
The company’s “About Us“ page helpfully explains the Eureka moment that prompted Elichai to create the company:
Carbyne was founded in 2015 by Amir Elichai after a personal experience revealed a critical gap in emergency communication. After being robbed at the beach, Amir called local emergency services—only to discover they couldn’t verify his location or send immediate help. This moment highlighted the disconnect between modern communication technology and outdated emergency response systems.
What Carbyne’s “About Us” page unhelpfully leaves out, however, is Elichai’s background. This was not some random mugging victim (assuming such a mugging ever actually took place). Rather, as Adam Bensaid reported for TRT World back in 2019, Elichai was “a distinguished member of Israel’s elite military intelligence group.” And he wasn’t the only “ex”-Israeli intelligence official on the company’s board. The company’s co-founder, Lital Leshem, was still a reservist in the Israeli Defense Force at the time he helped start Carbyne; Alex Dizengof, the company’s Chief Technology Officer, was previously responsible for cybersecurity in Israel’s Prime Minister’s office; and, as Bensaid also reports, the company’s first director had his own link to Israeli intelligence.
Pinchas Berkus, a former Brigadier General of the elite 8200 unit, was part of the Israeli Intelligence Corps responsible for signals intelligence and decryption, until he came to serve in Carbyne as a company director.
So, what is Unit 8200, exactly? As I explained in “Beyond Pegasus: The Bigger Picture of Israeli Cyber Spying,” my 2021 editorial on Israel’s military-grade “Pegasus” spyware:
For those who don’t know, Unit 8200 is the branch of the Israel Defense Force responsible for signals intelligence—i.e., Israel’s equivalent of the NSA. Supposedly founded in 1952 (or was it the 1930s?), the unit was not officially acknowledged until the early 2000s, when stories of the incredible (and incredibly illegal) acts of cyber espionage it has perpetrated over the decades began to be publicized.
And what acts of cyber espionage have Unit 8200 been involved in, exactly? How about acts such as:
- the development of Stuxnet, the military-grade cyberweapon that specifically targeted Iran’s nuclear enrichment facility at Natanz and that was confirmed to have been worked on by Unit 8200;
- the development of a radar “kill switch” that allowed Israel to bypass Syrian air defenses in their 2007 strike on a suspected nuclear reactor in that country;
- helping Israeli intelligence murder numerous civilians in Lebanon and Syria by implanting explosives in thousands of pagers, walkie-talkies and other electronic devices and remotely detonating them;
- partnering with Microsoft to create a system for storing personal data on millions of Palestinians—data that was then used to justify blackmail, administrative detentions and killings.
There are doubtless many other examples of perfidy and war crimes perpetrated or enabled by Unit 8200, but, given that it is an intelligence agency, such actions are still heavily classified.
Arguably more important than the operations Unit 8200 members conduct while still active members of the organization, however, are the companies they form after leaving the spy unit. As one 8200 veteran, Avishai Abrahami, told Forbes in 2016, the prevelance of “ex”-8200 members in Silicon Valley is by now impossible to ignore: “Just from my generation, there are more than 100 guys from the unit that I personally knew who built startups and sold them for a lot of money.”
Again, as I reported in “Beyond Pegasus“:
From communication companies like AudioCodes and Viber to cybersecurity companies like Argus and CheckPoint to GPS navigation software services like Waze, the prevalence of Unit 8200 alumni in the private tech sector has received so much press that even trade publications have been forced to report on the matter, noting that the Israeli military is increasingly outsourcing cybersecurity and intelligence projects to companies “that in some cases were built for this exact purpose.”
The companies formed by these “former” 8200 operatives include not just Carbyne, but Comverse Infosys (yes, that Comverse Infosys), Cybereason (yes, that Cybereason), Toka (yes, that Toka) and, of course, the NSO Group (yes, that NSO Group).
The fact that so many high-tech Israeli companies at the heart of America (and the world’s) emergency responses, communication infrastructure, payment systems and digital forensic tools have been founded by military-trained Israeli cyber intelligence officers should tell us something. Namely, that these apps, devices and spyware systems are vital tools of the trade for would-be spies in the 21st century.
Yes, as the Epstein/Thiel/Barak/Elichai nexus found in the Epstein files themselves informs us, the growing importance of the Unit 8200 gang in the heart of the global cybersecurity industry reflects a fundamental change that has taken place in intelligence in recent decades. In short, the spooks and spies are moving away from the old-school flesh-and-blood-style sexpot honeytraps that characterized the Epstein era of espionage and moving toward the Palantir-esque panopticon backdoor surveillance that characterizes the post-Epstein era of espionage.
FROM HONEYTRAPS TO PANOPTICON
Anyone who’s been paying even cursory attention to the workings of the kakistocracy over the past century will know that good old-fashioned blackmail has worked to ensure the deep state’s control over their puppets in the surface state for decades if not centuries (if not millennia). And no blackmail works as well as sexual blackmail.
We know, for instance, that J. Edgar Hoover had blackmail on every political player of consequence in Washington during his nearly half-century tenure as director of the FBI, including (it is alleged) the Kennedy brothers. And we know that others had blackmail on Hoover regarding his own taboo sexual practices.
We know the FBI tried to pressure Martin Luther King into committing suicide by threatening to release the audio tapes of his affairs with various women.
We know the KGB used a honeytrap to blackmail John Vassall, a British civil servant, into spying for the Soviet Union.
And readers of Whitney Webb’s One Nation Under Blackmail will know about the many, many ways that those in and around power in American politics have been steered into compromising positions for the purpose of being put under the thumb of various criminal elements.
Of course, these are just a few of the examples of sexual blackmail that we know about and have documentary evidence of. There are many, many more examples about which we have only the outline of the story.
But throughout the long, sordid history of blackmail, there has always been the need for would-be blackmailers to find, entice, record and recruit the target in question. Hitherto, this has required would-be blackmailers to engage in elaborate setups, including bringing targets to facilities that have been bugged with recording devices.
As successful as such tactics have historically proven to be, they are undoubtedly difficult, cumbersome and unreliable. A target with anything approaching a degree of discretion or basic training in espionage would likely recognize that they were being led into a honeytrap long before the trap could be sprung.
As the Epstein files also demonstrate, as often as Epstein and Maxwell were able to lure wealthy and powerful figures into their orbit and entice them to the island or the ranch or the Manhattan apartment, they were just as often unsuccessful in digging their talons into their target. There were many would-be victims of Epstein’s blackmail operation who sensed that something was off and rejected his or Ghislaine’s advances. Such are the vagaries of these meatspace blackmail operations.
But in our current digital dystopia, such tactics aren’t necessary. At this point, everyone is carrying a tracking and recording device with them 24/7. Any intel agent in a position to monitor those devices through spyware backdoors and to record the conversations of any target at any time with the simple click of a button would be able to find plenty of blackmail material on that target without the need for an elaborate Epstein-type honeytrap operation.
And, wouldn’t you know it, the development of just such spyware technology is exactly what Israeli intelligence has been working on feverishly.
With Comverse InfoSys, an Israel-based, Israeli-backed, Israeli-run company was able to wiretap phone communications in the US for decades.
With Pegasus, an Israeli spyware company was able to help governments in numerous countries snoop on their dissenters through their smartphones.
With Toka, Israel offered a “one-stop hacking shop for governments“ to help spooks around the world spy on people through their “Internet-of-Things” devices, including Wi-Fi connected security devices.
Of course, there would be one obvious way to diminish the influence of these Israeli cyber spies: governments could stop giving contracts to companies founded by “ex”-Israeli intelligence operatives.
In the wake of the Pegasus spyware scandal in 2021, there was a moment where it looked like the EU was actually going to do the bare minimum to clear this incredibly low threshold of “action” on the spyware subject. After a European Parliament committee examining the use of spyware in Europe issued a blistering report condemning the NSO Group (the company that developed the Pegasus spyware) and Black Cube (a private Israeli intelligence agency comprised of former Mossad members) by name, European Parliament took the bold step of…”Setting spyware standards“ for EU states to follow. If they feel like it. Even the EU’s cheerleaders had to admit that the parliament’s totally ineffectual response means that it will continue to be business as usual for the (mostly Israeli) spyware industry.
And—whodathunkit?—those detractors have been proven right. Just last summer, the EU was struck with yet another spyware scandal. This time, Paragon Solutions, a “US-backed Israeli company,” was caught helping the Italian government spy on three prominent European journalists.
So, how about Uncle Sam? In a move that will surprise precisely no one, the US government has now doubled down on its reliance on Israeli-produced spyware. In fact, as Reuters reported last month, the Trump administration is actively working to remove sanctions on Israeli spyware-linked executives.
President Donald Trump’s administration has lifted sanctions on three executives tied to the spy software consortium Intellexa, according to a notice published to the U.S. Treasury’s website. The move partially reverses the imposition of sanctions last year by then-President Joe Biden’s administration on seven people tied to Intellexa. The Treasury Department at the time described the consortium, launched by former Israeli intelligence official Tal Dilian, as “a complex international web of decentralized companies that built and commercialized a comprehensive suite of highly invasive spyware products.”
But don’t worry, Americans. Rather than outsourcing all the spying to Israel, US companies are now looking to get in on the post-Epstein surveillance dragnet…by buying up sanctioned Israeli spyware companies.
In an article last year on how “America now leads the world in surveillanceware investment,” The Register reported on one such Israeli surveillanceware company, Saito Tech Ltd, which was sanctioned by the US Commerce Department in 2021 “based on evidence that these entities developed and supplied spyware to foreign governments that used these tools to maliciously target government officials, journalists, businesspeople, activists, academics, and embassy workers.”
After the sanction, US investors didn’t shy away from the sanctioned company. Instead, they bought it out.
That didn’t stop US biz Integrity Partners from buying the company behind [the sanctioned spyware] for $30 million in April, after the company reorganized its intellectual property rights, making the sale technically legal under American law.
Yes, spyware is big business, and every government wants a piece of the action. It just so happens that Israeli intelligence has just about cornered the market. Ergo, any government wanting to spy on their citizens needs to cut Israel in on the deal.
Given all of this information, it’s no surprise that signs of the changeover in intelligence methods from real-world honeytraps to cyber surveillance are to be found in the Epstein files. Perhaps the only real surprise here is that it took so long for the powers-that-shouldn’t-be to realize Epstein was becoming more of a liability than an asset and to take measures to tie up that loose end.
____
https://corbettreport.substack.com/p/israeli-spying-after-epstein
